Enterprise Architecture (EA) frameworks provide the blueprint for organizational structure and IT strategy. The Open Group Architecture Framework (TOGAF) stands as a leading standard for this discipline. However, a robust architecture cannot exist without a strong security foundation. Security is not a bolt-on feature; it is an intrinsic component of the system design. Integrating security architecture within the TOGAF Architecture Development Method (ADM) ensures that risk management, compliance, and data protection are addressed at every stage of development.
This guide details how to embed security considerations into the ADM cycle. We explore the specific activities, artifacts, and security concerns relevant to each phase. By following this structured approach, architects can build resilient systems that withstand threats while meeting business objectives.
🏗️ The Foundation: Security and TOGAF
Security Architecture focuses on the design, implementation, and management of security controls within an IT environment. When aligned with TOGAF, security moves from an afterthought to a core architectural pillar. The ADM cycle is iterative, allowing security to be refined and updated as the architecture evolves.
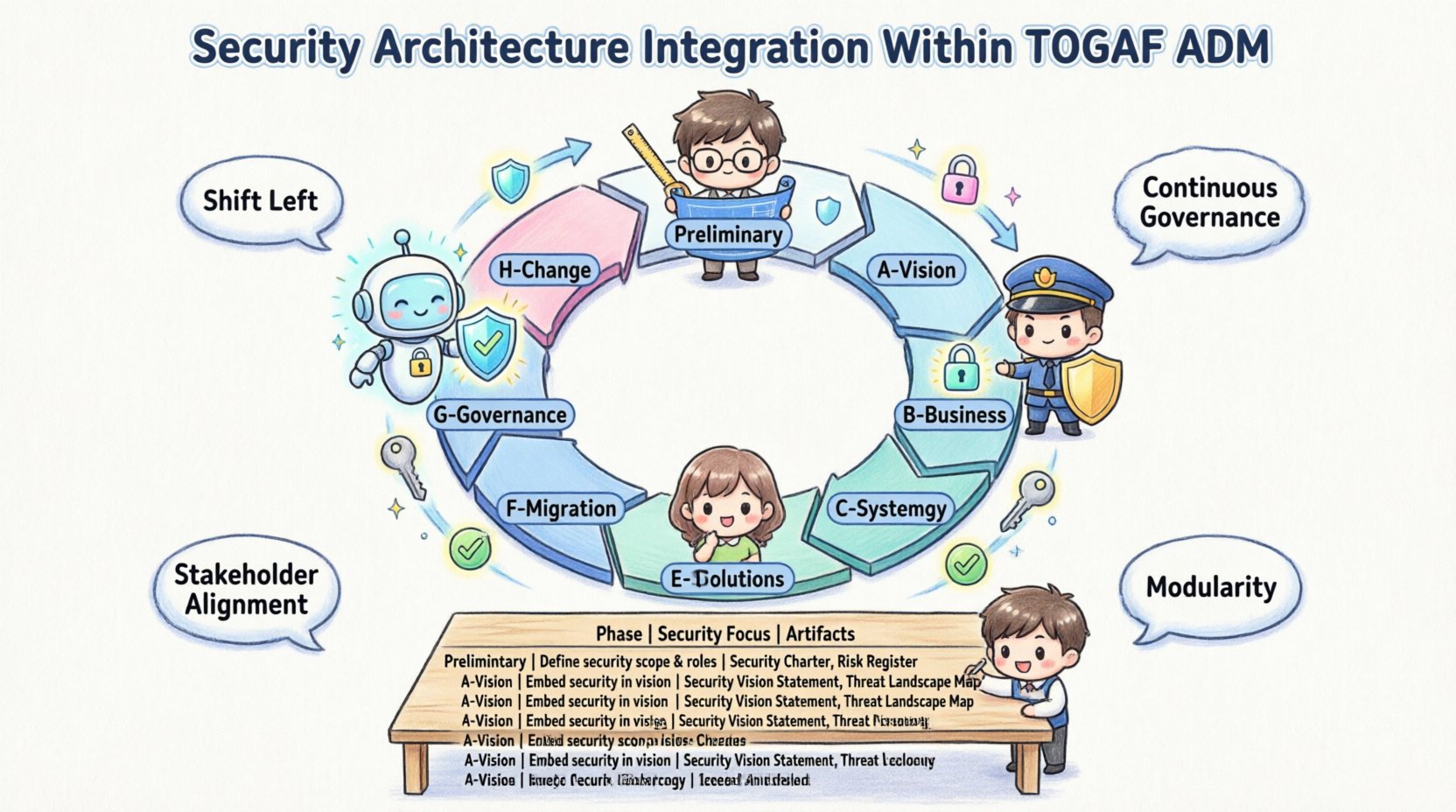
Key principles for integration include:
- Shift Left: Address security requirements during the initial planning phases, not during implementation.
- Continuous Governance: Security oversight must persist from vision to maintenance.
- Stakeholder Alignment: Security goals must align with business risks and compliance mandates.
- Modularity: Security controls should be reusable components across different domains.
📋 TOGAF ADM Phases and Security Activities
The ADM consists of several distinct phases. Each phase has specific deliverables where security must be explicitly addressed. Below is a breakdown of how security integrates into each step.
🔹 Preliminary Phase: Defining the Framework
The Preliminary Phase sets the stage for the enterprise architecture work. It defines the principles and capabilities needed for the organization.
- Security Principles: Define principles such as “Security by Design” or “Least Privilege Access.” These principles guide all subsequent decisions.
- Security Capability: Assess the current maturity of security practices. Identify gaps in skills, tools, and processes.
- Architecture Repository: Ensure the repository stores security artifacts securely and manages access to them.
🔹 Phase A: Architecture Vision
Phase A establishes the scope and constraints of the project. Security must be part of the initial vision.
- Business Drivers: Identify regulatory requirements (e.g., GDPR, HIPAA) that dictate security needs.
- Stakeholder Concerns: Engage security stakeholders early. Their concerns regarding data privacy and access control must be recorded.
- Statement of Architecture Work: Include security milestones and governance requirements in the scope document.
🔹 Phase B: Business Architecture
Security in the Business Architecture phase focuses on how security processes support business functions.
- Process Security: Map business processes to identify where sensitive data is handled.
- Role-Based Access Control (RBAC): Define business roles that require specific security permissions.
- Risk Assessment: Conduct initial risk assessments to understand threats to business operations.
🔹 Phase C: Information Systems Architectures
This phase covers Data Architecture and Application Architecture. It is often where the most critical security decisions are made.
Data Architecture Security
- Data Classification: Categorize data based on sensitivity (Public, Internal, Confidential).
- Encryption Standards: Define requirements for data at rest and data in transit.
- Privacy: Ensure data lineage supports privacy regulations and right-to-be-forgotten requests.
Application Architecture Security
- Authentication & Authorization: Design the identity management flow across applications.
- Input Validation: Ensure application interfaces are designed to prevent injection attacks.
- API Security: Define protocols for securing service-to-service communication.
🔹 Phase D: Technology Architecture
Phase D focuses on the hardware and software infrastructure required to support the applications.
- Network Segmentation: Design network zones to isolate sensitive systems.
- Infrastructure Hardening: Specify configuration standards for servers and network devices.
- Secure Protocols: Mandate the use of secure communication protocols (e.g., TLS 1.2+).
- Logging & Monitoring: Plan for centralized logging to support incident detection.
🔹 Phase E: Opportunities and Solutions
This phase identifies the building blocks and projects needed to achieve the target architecture.
- Security Building Blocks: Select security components that align with the defined standards.
- Implementation Roadmap: Schedule security implementation tasks alongside functional deliverables.
- Gap Analysis: Compare the baseline security state with the target security state.
🔹 Phase F: Migration Planning
Migration Planning details the transition from the baseline to the target architecture.
- Security Migration Strategy: Define how legacy security controls will be decommissioned safely.
- Transition Architectures: Ensure intermediate states maintain security posture during transition.
- Resource Allocation: Assign budget and personnel for security testing and auditing.
🔹 Phase G: Implementation Governance
Phase G oversees the actual build and deployment of the architecture.
- Compliance Auditing: Verify that the implementation matches the security architecture.
- Change Management: Evaluate security impacts of any changes proposed during implementation.
- Architecture Compliance: Ensure developers adhere to security coding standards.
🔹 Phase H: Architecture Change Management
Once the architecture is live, it requires maintenance and evolution.
- Vulnerability Management: Monitor for new threats that require architectural changes.
- Security Updates: Plan for periodic updates to security controls as standards evolve.
- Feedback Loop: Use operational data to refine the security architecture.
📊 Mapping Security Activities to ADM Phases
To visualize the integration, refer to the table below. It outlines the primary security focus for each phase of the ADM.
| Phase | Primary Security Focus | Key Security Artifacts |
|---|---|---|
| Preliminary | Principles & Capability | Security Principles, Security Capability Assessment |
| A | Scope & Compliance | Architecture Vision, Risk Register |
| B | Process & Roles | Business Process Security, Role Definitions |
| C | Data & Application | Data Classification, Authentication Patterns |
| D | Infrastructure & Network | Network Segmentation, Hardening Standards |
| E | Solutions & Gaps | Security Gap Analysis, Solution Portfolio |
| F | Transition Planning | Migration Plan, Security Rollout Schedule |
| G | Governance & Audit | Compliance Reports, Implementation Reviews |
| H | Evolution & Maintenance | Vulnerability Reports, Change Requests |
🛡️ Security Governance and Compliance
Governance ensures that the security architecture remains effective over time. The TOGAF Architecture Board often handles this, but a dedicated Security Architecture Board can provide specialized oversight.
Establishing Governance Mechanisms
- Review Boards: Create a forum where security changes are reviewed before approval.
- Standards Compliance: Map internal standards to external regulations.
- Metrics and KPIs: Define key performance indicators for security posture, such as time to patch or incident response time.
Managing Risks
Risk management is continuous. It involves identifying, assessing, and treating risks throughout the lifecycle.
- Threat Modeling: Use threat models to predict potential attack vectors in the design.
- Risk Acceptance: Define who has the authority to accept residual risk.
- Incident Response: Integrate incident response plans into the architecture design.
⚠️ Common Challenges and Solutions
Integrating security into TOGAF can present hurdles. Understanding these common issues helps architects navigate them effectively.
| Challenge | Impact | Proposed Solution |
|---|---|---|
| Late Security Involvement | Costly rework and design flaws | Include security architects in Phase A and B. |
| Complexity Overload | Confusion and stalled progress | Use simplified security patterns for common scenarios. |
| Compliance Silos | Conflicting requirements | Consolidate compliance requirements into a single security baseline. |
| Legacy Systems | Inability to apply modern controls | Implement compensating controls and network isolation. |
| Lack of Metrics | Inability to prove value | Define clear security metrics tied to business value. |
🚀 Best Practices for Security Integration
To ensure a successful integration of security within the TOGAF ADM, adopt these practices.
- Define a Security Architecture Statement: Create a document that outlines the security strategy and standards for the enterprise.
- Automate Where Possible: Use automated tools for compliance checking and vulnerability scanning within the architecture repository.
- Train the Team: Ensure all architects understand the security principles and how to apply them.
- Iterate Frequently: Security is not a one-time activity. Revisit the architecture regularly to adapt to new threats.
- Document Decisions: Record the rationale behind security choices in the Architecture Repository for future reference.
🔗 The Role of the Security Repository
The TOGAF Architecture Repository is a central store for all architecture artifacts. A dedicated Security Repository section is vital.
- Access Control: Ensure only authorized personnel can view sensitive security documents.
- Versioning: Maintain version history for security policies and standards.
- Linkage: Link security artifacts to business processes and technical specifications.
🔄 Iteration and Feedback Loops
The ADM is not linear. It is cyclical. Security must be evaluated at every iteration.
- Phase A Review: Does the vision still align with security goals?
- Phase C/D Review: Do the technical designs meet the security requirements?
- Phase G Review: Is the implementation compliant with the design?
🔍 Measuring Success
How do you know if security integration is working? Look for indicators of maturity.
- Reduced Incidents: Fewer security breaches related to design flaws.
- Faster Compliance: Quicker audit cycles due to clear documentation.
- Stakeholder Confidence: Business leaders trust the architecture to handle sensitive data.
- Cost Efficiency: Lower costs associated with fixing security issues post-deployment.
🏁 Final Thoughts on Secure Architecture
Security architecture within TOGAF is a discipline that requires careful planning and continuous attention. It is not about adding barriers; it is about building trust into the system design. By embedding security into the ADM phases, organizations create a resilient foundation for their digital transformation.
Architects must remain vigilant. Threats evolve, and so must the architecture. The framework provides the structure, but the commitment to security provides the strength. Start with the principles, document the requirements, and govern the implementation. This ensures that security is woven into the fabric of the enterprise, supporting business goals while protecting assets.
Remember that architecture is a living document. As the organization grows, the security architecture must grow with it. Regular reviews and updates are essential. Maintain the repository, keep the standards current, and engage the stakeholders. Through this disciplined approach, the enterprise achieves a secure and sustainable future.
